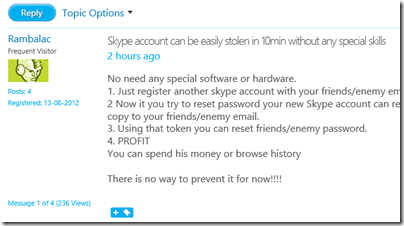
Today there are reports of a breathtakingly bad vulnerability in Skype, that allows anyone to hijack another person’s account simply by knowing the email.
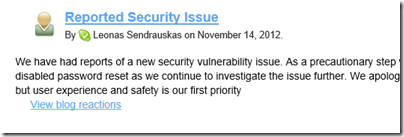
Password resets have now been disabled, fixing the problem temporarily, but it remains inexcusable.
It is basic security practice that ownership of an email address must be validated with a confirming email to that address and a special link. I see this on web forums that discuss trivia – why not on Skype where you can spend real money, and more seriously, see contacts and conversation history?
There must be a second weakness here, in that somehow the new account ends up getting confused (by Skype) with the existing one. It should not be possible to create an account with an email address that is in use on another account. Actually I count three weaknesses:
1. You can create an account with an email address that is not validated.
2. You can create an account with an email address that is already in use on another account.
3. You can reset the password on another account without having access to their email address, by resetting it on a second account with the same email address.
Microsoft acquired Skype in October 2011 but it is not clear when this vulnerability was introduced.
I tested this myself by setting up a new account with an email address that already has a Skype account. It worked though I did not take it to the next stage. Now I have a Skype account, incidentally, which cannot be deleted as Skype does not allow this. However I have now reset the email.
As it happens, I have suffered in the past from people opening accounts with my email address, I believe because of innocent error, such as forgetting to type the number in an account like someoneNN@yahoo.com or the like. One person set up an Apple iTunes account with my email address, complete with credit card details. I complained to Apple who disabled the account, but as with Skype, it cannot be deleted. So if I ever want to use that email address for an Apple account I will have problems.
That was a few years ago. It is astonishing that a company the size of Skype/Microsoft, handling and storing vast amounts of personal information, would have such weaknesses in its security.
Who will trust Skype now?
Update: It also appears that this flaw, or part of it, was reported to Skype back in August. This is a failure of management as well as security.
People giving others’ email addresses are an insidious problem. Time ago I was one of the first subscribers of an ISP. I thought I’d been lucky to get a short, clean address “nico@thatisp.es”. But then I started to receive all kind of strange email, the most bizarre intended for some gay person, including explicit photos of scotsmen (don’t ask) and lots of intimate conversations. I alerted the sender, but it took him months to accept that I was not his friend and I had no idea what the real address was.
Now I have a less generic address (still I share name with a known gay pornstar, but he doesn’t seem to use GMail) but some other person gave my address (instead of the correct “niko” one) to his jogging club. Less embarrassing, but many more messages.
Since they use the email-list ad hoc method of “reply to all”, every attemp to reason with them was utterly useless. I had to flag every message as spam until I stopped receiving them, because individually blocking addresses was a PITA.
I haven’t trusted Skype for **seven years**. Ever since I read about the code obfuscation techniques that they used to defeat reverse-engineering.
See, e.g., http://www.ossir.org/windows/supports/2005/2005-11-07/EADS-CCR_Fabrice_Skype.pdf
That just gave me a really bad feeling. It just reminded me too much of the Eastern European hacker mindset, where you work at a much deeper level in the system than you actually need. It’s great for telling stories at conferences about how clever you are, but it makes for a far greater likelihood of bugs — including security bugs.
It also gives you a false feeling of confidence — because your code is so difficult to reverse-engineer, you might let your guard down and fall prey to more basic security vulnerabilities.
Frankly, I was shocked that Skype was able to pass the security code reviews at Microsoft. Did they even do proper due diligence on the codebase before acquiring Skype?
Granted, the current breach is on the website — not the client. But it’s consistent with the fears that I had about Skype. If a company hasn’t demonstrated a good security mindset in one area, then it’s likely to fall short in other areas, too.
I don’t know what I’m going to do now that Windows Messenger is being replaced by Skype …