Microsoft has released a Web Standards Update for Visual Studio 2010, with new HTML5, CSS3 and JavaScript support.
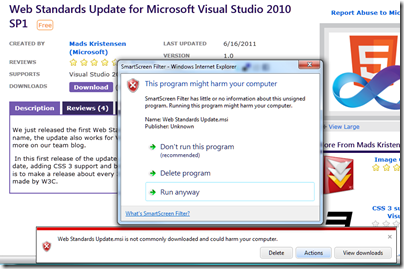
I look forward to trying it; but Internet Explorer 9’s Smart Filter was not keen.
What you cannot see from the screenshot is that the option to “Run anyway” is hidden by default. You have to click More Options; otherwise you just get the first two options, Don’t run, or Delete.
Note that this download is from an official Microsoft site, and has been downloaded, according to the stats on the page, nearly 6,500 times.
Developers can cope; but I think this sort of warning is extreme for a download from an official Microsoft site, whose main crime is being unknown, for some reason, to the SmartScreen database of approved executables.
Though maybe the Visual Studio team should have signed the installer.
The long term effect is that we learn to ignore the warnings. Which is a shame, because the next one might be real.
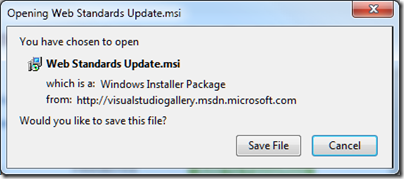
Update: How do other browsers handle this scenario? Here’s Google Chrome:
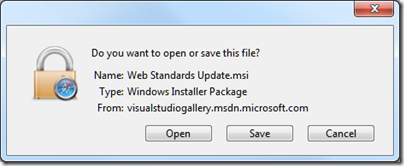
Mozilla Firefox – a prompt, not a warning:
same in Apple Safari:
Which is best? Well, IE9 wins kudos for being the only browser to point out that the package is unsigned; but loses it for its over-the-top reaction. Chrome has pitched the leverl of warning about right; Firefox and Safari are perhaps too soft, though let’s also allow for the fact that their filters may already have worked out that thousands had already downloaded this file without known incident so far.
The IE9 issue is mainly because the installer package is unsigned, which is probably an oversight that will be fixed soon.
Users ignore security warnings because they’ve been trained by thousands upon thousands of applications that throw up dialogs with technobabble. Since users want to get things done, they click “Okay”, or “Cancel” if the dialog is particularly scary.
Security warnings are few and far between (or at least should be), but crappy UI and UX are ubiquitous.
How is the FF warning too soft? You have to run the thing manually…
User is very likely to run it after download. The idea of these filters and warnings is to catch malware before it is downloaded. The OS has its own security measures of course.
Tim
False positives is understated. Some people distribute programs that will almost never be downloaded, because they aren’t intendd to. I had made a Vbasic program to allow access to an adminCP on my site. Of course, it will never be downloaded by more then 4 people, so every time will be blocked.
It didn’t even give me the option to RUN Anyway. It just deleted it.
Actually, this wasn’t an official MS update to VS2010. It WAS created by three guys who work at MS, yes but it was not an official update. Check this blog for more info: http://www.hanselman.com/blog/AnnouncingTheWebStandardsUpdateHTML5SupportForTheVisualStudio2010Editor.aspx and this later post from the same blog: http://www.hanselman.com/blog/UsingCodeSigningCertificatesToSignDownloadedMSIsAndBuildReputationWithIE9SmartScreen.aspx
This kind of security is like an airport allowing only staff and loyal customers. They block all terrorists, but also casual passengers. Is this good or bad? Ask the angry crowd at the airport’s gate.