A friend called on Christmas day. She was away from home and had forgotten to set the video to record a couple of TV programmes. We’re testing Vista media center, so it was a matter of going to Vista’s TV guide, scrolling to the programmes she wanted, and selecting Record. What about the transfer to DVD? Next day, I selected Recorded TV, and scrolled through the recordings, each of which has a preview image. When I found the right one, I clicked on it and noticed that Burn CD/DVD was one of the menu choices. So I stuck a blank DVD -R in the drive, clicked Burn CD/DVD, and a while later (quite a long while) it was done. Tested the DVD in a standalone DVD player and it worked fine. I don’t miss VHS one bit.
Now have a read of Peter Gutmann’s Cost Analysis of Windows Vista Content Protection. Gutmann is a security specialist who describes himself as a professional paranoid, which perhaps explains the tone of the piece – he calls Vista’s content protection a “suicide note”. I doubt he is correct in all his conclusions, but nevertheless it shines a fascinating spotlight on this aspect of Windows Vista.
It has always been possible to make unlicensed copies of media such as music and film, but in the pre-digital world it was inconvenient and always involved some loss of quality. Personal computers changed all that, particularly when combined with the cheap storage which we now have in abundance. This is bad news for industries that depend on selling this content rather than giving it away. Hence Vista tries to put media back into its uncopyable box, so that once again you have to purchase the official item.
A single pinprick is enough to burst a balloon, no matter how airtight the rest of it is. Similarly, to protect media you have to protect every link in the chain, from digital source to final output. Vista calls this the Protected Media Path; read the MSDN article here. The system is intricate and complex, and as Gutmann notes there are undesirable implications. The Protected Environment (PE) relies on “trusted components” such as drivers, codecs and content processors. Each component must therefore be signed by Microsoft after a verification process. But what if a bug or design flaw has slipped through, allowing content to be pirated (a pinprick)? Then the component can be “revoked”, which means some hardware or feature in your system will no longer work properly. Content publishers can even specify that their content will not play if a component known to be unsafe is present, by checking against a revocation list.
Ideally, a revoked component will be replaced by an automatically downloaded update. However, Microsoft’s document on the subject acknowledges that this may not always be the case:
In rare cases, an updated version of the component may not be available, for example, the company that implemented the component has gone out of business. If the component is not essential, the PE can work around the issue by not loading the component. If the component is essential, the application is provided with a URL that directs the user to a Web page that has information on the issue.
That might mean no more protected content for you unless you actually replaced the hardware with something else for which trusted components exist. I presume however that you would still be able to play unprotected content. Still, this would be a severe outcome if, for example, you had a large collection of HD-DVD movies that you played on the system.
It is understandable if hardware vendors such as ATI are unenthusiastic about all this. They have to do the work of creating suitable hardware and drivers, but the beneficiaries are the owners of the protected content.
Several obvious questions come to mind:
- Will this really work? Such a complex system must be vulnerable to the efforts of determined hackers, as other DRM schemes have been in the past.
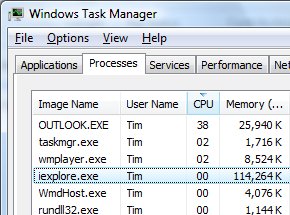
- When playing protected content, what are the performance implications?
- How about when playing unprotected content ? What, if any, is the performance impact of all this content protection then? Perhaps there is none. It strikes me though that there could be unwanted side-effects.
The existence of this DRM edifice also impacts all of us as consumers. When we purchase content, we’d like to be able to play it on as many devices as possible: home stereo, wireless streaming around the house, computers, portable devices. Technology is at last enabling this freedom, but now technology is also taking it away.
I’ll come back to where I started. Whether Vista content protection stands or falls will depend on the user experience. If it is good, as with my DVD burning from media center, then consumers will forgive a lot, to the frustration of anti-DRM advocates. That’s why Apple gets away with the iTunes store/iPod lock-in. If it is bad, this will damage Vista and Microsoft.
Update
Interesting thread here on audio processing in Vista. Here’s what Amir Majidimehr, digital media VP at Microsoft, has to say about DRM in Vista audio (and referring specifically to Gutmann’s piece):
The writer unfortunately, is misinformed about the Vista content protection capabilities. Yes, it is true that Vista has a substantially upgraded *infrastructure* for content protection. However, its usage is optional and no application is forced to use it. To wit, current HD DVD/BD players do not use any of it and as such, are only subject to provisions of copy protection for those formats (namely, AACS). Ditto for any third-party application that you may run on Vista. As long as they don’t call the new facilities, they run as they did always.
So for all practial purposes, Vista and XP behave the same wrt to playback of digital media.
Vista does allow new applications to provide a new level of robustness against attacks should they wish to provide this level of content protection. That may enable them to get access to content that would not be available otherwise (think HD downloads near Theater release window). As this feature required core operating system changes, we incorporated them into Vista. As with all new facilities, it may be years before they are taken advantage of.
That’s reassuring with respect to my third question above.