Yesterday I attended a UK Microsoft MMS catch-up session in Manchester, aimed at those who could not make it to Las Vegas last month. The subject was the new System Center 2012, and how it fits with Microsoft’s concept of the private cloud, and its strategy for supporting Bring Your Own Device (BYOD), the proliferation of mobile devices on which users now expect to be able to receive work email and do other work.
The session, I have to say, was on the dry side; but taken on its own terms System Center 2012 looks good. I was particularly interested in how Microsoft defines “private cloud” versus just a bunch of virtual machines (JBVM?). Attendees where told that a private cloud has four characteristics:
- Pooled resources: an enterprise cloud, not dedicated servers for each department.
- Self service: users (who might also be admins) can get new server resources on demand.
- Elasticity: apps that scale on demand.
- Usage based: could be charge-back, but more often show-back, the ability to report on what resources each user is consuming.
Microsoft’s virtualization platform is based on Hyper-V, which we were assured now represents 28% of new server virtual machines, but System Center has some support for VMWare and Citrix Xen as well.
System Center now consists of eight major components:
- Virtual Machine Manager: manage your private cloud
- Configuration Manager (SCCM): deploy client applications, manage your mobile devices
- Operations Manager: monitor network and application health
- Data Protection Manager: backup, not much mentioned
- Service Manager: Help desk and change management, not much mentioned
- Orchestrator: a newish product acquired from Opalis in 2009, automates tasks and is critical for self-service
- App Controller: manage applications on your cloud
- Endpoint protection: anti-malware, praised occasionally but not really presented yesterday
I will not bore you by going through this blow by blow, but I do have some observations.
First, in a Microsoft-platform world System Center makes a lot of sense for large organisations who do not want public cloud and who want to move to the next stage in managing their servers and clients without radically changing their approach.
Following on from that, System Center meets some of the requirements Microsoft laid out as the start of the session, but not all. In particular, it is weak on elasticity. Microsoft needs something like Amazon’s Elastic Beanstalk which lets you deploy an application, set a minimum and maximum instance count, and have the platform handle the mechanics of load balancing and scaling up and down on demand. You can do it on System Center, we were told, if you can write a bunch of scripts to make it work. At some future point Orchestrator will get auto scale-out functionality.
Second, it seems to me unfortunate that Microsoft has two approaches to cloud management, one in System Center for private cloud, and one in Azure for public cloud. You would expect some differences, of course; but looking at the deployment process for applications on System Center App Controller it seems to be a different model from what you use for Azure.
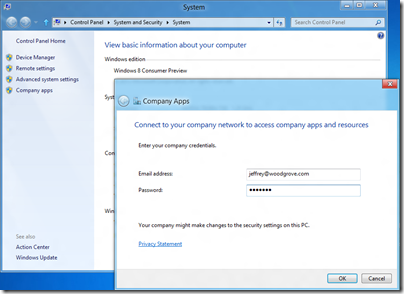
Third, System Center 2012 has features to support BYOD and enterprise app stores, and my guess is that this is the way forward. Mobile device management in Configuration Manager uses a Configuration Manager Client installed on the device, or where that is not possible, exploits the support for Exchange ActiveSync policies found in many current smartphones, including features like Approved Application List, Require Device Encryption, and remote wipe after a specified number of wrong passwords entered.
The Software Center in Configuration Manager lets users request and install applications using a variety of different mechanisms under the covers, from Windows Installer to scripts and virtualised applications.
Where this gets even more interesting is in the next version of InTune, the cloud-based PC and device management tool. We saw a demonstration of a custon iOS app installed via self-service from InTune onto an iPhone. I presume this feature will also come to Software Center in SCCM though it is not there yet as far as I aware.
You can also see this demonstrated in the second MMS keynote here – it is the last demo in the Day 2 keynote.
InTune differs from System Center in that it is not based on Windows domains, though you can apply a limited set of policies. In some respects it is similar to the new self-service portal which Microsoft is bringing out for deploying Metro apps to Windows RT (Windows on ARM) devices, as described here.
This set me thinking. Which machines will be easier to manage in the enterprise, the Windows boxes with their group policy and patch management and complex application installs? Or the BYOD-style devices, including Windows RT, with their secure operating systems, isolated applications, and easy self-service app install and removal?
The latter approach seems to me a better approach. Of course most corporate apps do not work that way yet, though app virtualisation and desktop virtualisation helps, but it seems to me that this is the right direction for corporate IT.
The implication is two-fold. One is that basing your client device strategy around iPads makes considerable sense. This, I imagine, is what Microsoft fears.
The other implication is that Windows RT (which includes Office) plus Metro apps is close to the perfect corporate client. Microsoft VP Steven Sinofsky no doubt gets this, which is why he is driving Metro in Windows 8 despite the fact that the Windows community largely wants Windows 7 + and not the hybrid Metro and desktop OS that we have in Windows 8.
Windows 8 on x86 will be less suitable, because it perpetuates the security issues in Windows 7, and because users will tend to spend their time in familiar Windows desktop applications which lack the security and isolation benefits of Metro apps, and which will be hard to use on a tablet without keyboard and mouse.