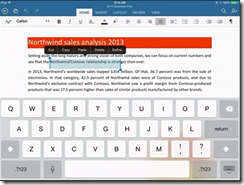
New Microsoft CEO Satya Nadella has announced Office for iPad at an event in San Francisco. Office General Manager Julie White gave a demo of Word, Excel and Powerpoint on Apple’s tablet.
White made a point of the fidelity of Office documents in Microsoft’s app, as opposed to third party viewers.
Excel looks good with a special numeric input tool.
Office will be available immediately – well, from 11.00 Pacific Time today – and will be free for viewing, but require an Office 365 subscription for editing. I am not clear yet how that works out for someone who wants full Office for iPad, but does not want to use Office 365; perhaps they will have to create an account just for that purpose.
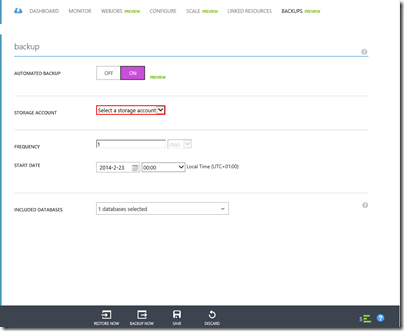
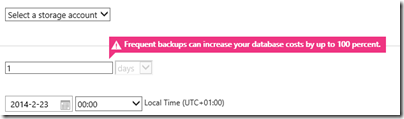
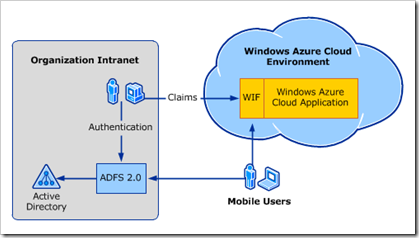
There was also a focus on Office 365 single sign-on from any device. This is Azure Active Directory, which has several key characteristics:
1. It is used by every Office 365 account.
2. It can be synchronised and/or federated with Active Directory on-premise. Active Directory handles identity and authentication for a large proportion of businesses, small and large, so this is a big deal.
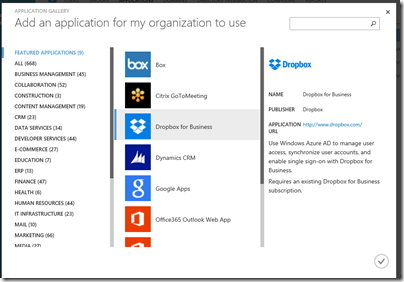
3. Developers can write apps that use Azure Active Directory for authentication. These can be integrated with SharePoint in Office 365, or hosted on Azure as a separate web destination.
While this is not new, it seems to me significant since new cloud applications can integrate seamlessly with the directory already used by the business.
Microsoft already has some support for this in Visual Studio and elsewhere – check out Cloud Business Apps, for example – but it could do more to surface this and make it easy for developers. Nadella talked about SDK support for iOS and other devices.
Microsoft hardly mentioned Android at the event, even though it has a larger market share than iOS. That may be because of the iPad’s popularity in the enterprise, or does it show reluctance to support the platform of a bitter competitor?
Microsoft is late with Office for iPad; it should perhaps have done this two years ago, but was held back by wanting to keep Office as an exclusive for Windows tablets like Surface, as well as arguments with Apple over whether it should share subscription income (I do not know how that has been resolved).
There was also a brief introduction to the Enterprise Mobility Suite, which builds on existing products including Azure Active Directory, InTune (for device management) and Azure Rights Management to form a complete mobility management suite.
Nadella made a confident performance, Office for iPad looks good.
What is coming up at Build, Microsoft’s developer conference next week? Nadella said that we will hear about innovations in Windows, among other things. Following the difficulties Microsoft has had in marketing Windows 8, this will be watched with interest.